Cloud Security Posture Management is a commodity
Beyond the classic CSPM tools like Dome9, DivvyCloud, etc. now even infrastructure and workload scanners claim CSPM as part of their capabilities. Cloud Security Posture Management capabilities should be evolving because cloud configuration management is only becoming more complex, instead we are seeing the same old misconfiguration checks coming out of every CSPM offering with no depth or flexibility to modify the monitoring rules. How can we monitor user defined configuration baselines? There are many configs that are unique to our cloud environment. How can we monitor more than just basic property checks such as the relationships between assets?
Cyber Asset Attack Surface Management is the evolution
CAASM can do everything CSPM does and more. Even though it's a mouthful of an acronym (I didn't invent it), CAASM goes beyond the basic cloud configuration checks and allows us to monitor custom configurations important to our unique security architecture. CAASM also visualizes and monitors our entire attack surface from the public cloud and beyond, exposing unique toxic combinations of misconfigurations and relationships that CSPMs simply cannot.
Here are 2 cloud attack surface monitoring use cases that JupiterOne can handle that any traditional CSPM cannot.
1) Identify all your assets and services that are accessible by any of your EC2 instances that are on publicly configured VPCs (publicly configured includes ACL, internet gateway, and routing table configs), and whose security groups allow public SSH ingress over TCP.
Think about how much effort it would typically take to determine the blast radius for this attack vector. Using JupiterOne I literally tweaked a question to find the result in 20 seconds. This is the power that every security engineering team needs at their fingertips. Not to mention I could set this up for continuous monitoring and trigger alerts workflows via API. Notice in the image how we can monitor the specific actions allowed on each service or resource.

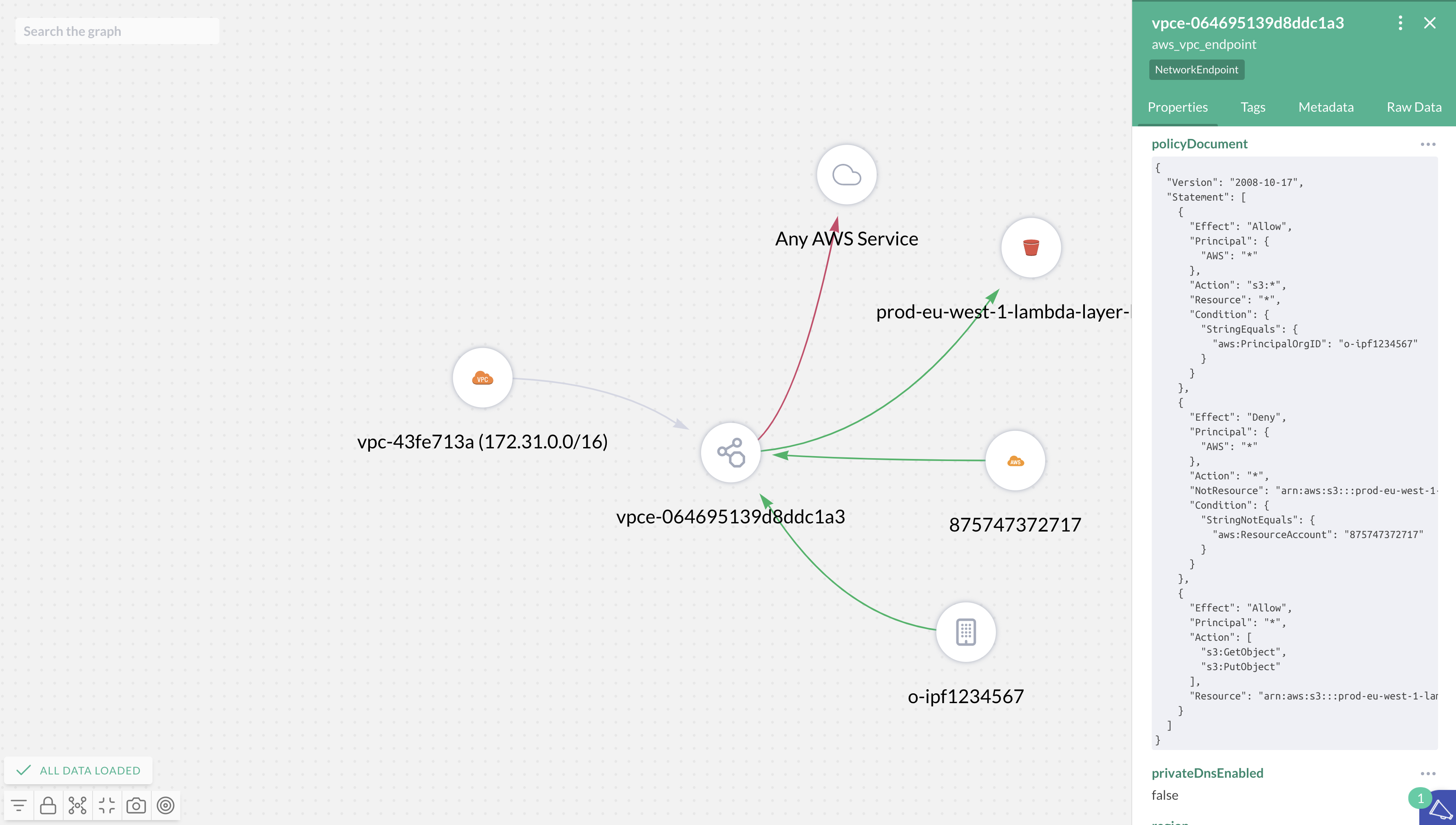
2) Identify the attack surface defined by all production VPCs and their respective VPC endpoint configurations (including all the services and resources allowed/denied).
VPCs are becoming the defacto mechanism for securing logical access to resources in AWS. VPC endpoint configs are extremely important and typically unique to each business. Monitoring vpc endpoint policies, internet gateway configs, VPC peering, route tables, ACLs, load balancers, cloud front distributions, NAT gateway configs, etc. should all be table-stakes for a cloud monitoring solution.
The query to monitor this attack surface in JupiterOne takes only a little effort to understand:
Find aws_vpc with tag.production=true
that has aws_vpc_endpoint
that (allows|denies) *
Notice how we parse the vpc endpoint policy as well and illustrate the connections. The allowed relationships are in green, the denied relationships are in red, and we will even note which relationships are allowed but rendered ineffective by a deny.
JupiterOne, Data Graph Model and Knowledge Graph Visualizations
JupiterOne's query language, graph data model, and knowledge graph visualizations allow users to define custom controls, and allow us to easily and automatically analyze complex attack surfaces. I haven't even talked about how we integrate with and connect your assets beyond the cloud into the same knowledge graph! JupiterOne can help manage the attack surface across an entire security program. I'll save that for a follow up blog, but please reach out if interested in hearing more.
Additional CAASM Resources and Related Blogs
- Next-Gen Cloud Security Posture Management | CSPM+
- The Definitive Guide to Cyber Asset Attack Surface Management
- CAASM Should Be an Early Security Investment in Every CISO's Playbook
- The Debate: Should You Build or Buy CAASM?
- The 3 Biggest Challenges of Cyber Asset Management and How to Solve Them
- Better Together: CMDB + CSPM = Cloud Native Cyber Asset Management
- A Modern Definition for Cyber Assets
- Gartner Hype Cycle for Security Operations, 2021









